Cracking The Code: Trey Anastasio Band’s ‘Paper Wheels’ Artwork
By Andy Kahn Apr 3, 2015 • 8:40 am PDT
When the new Trey Anastasio Band album Paper Wheels was announced, with it came a studio recording the new track “Bounce.” Since that initial announcement, two additional recordings, “Speak to Me” and “Never,” have been posted to the Phish frontman’s website. Sources say all three songs we be featured on the new album, which we can confirm is currently scheduled for an October 2015 release. The three songs, produced by Anastasio and Bryce Goggin and recorded at The Barn, share a similar full band sound and intriguing artwork designed by Matt Taylor accompanying their releases.
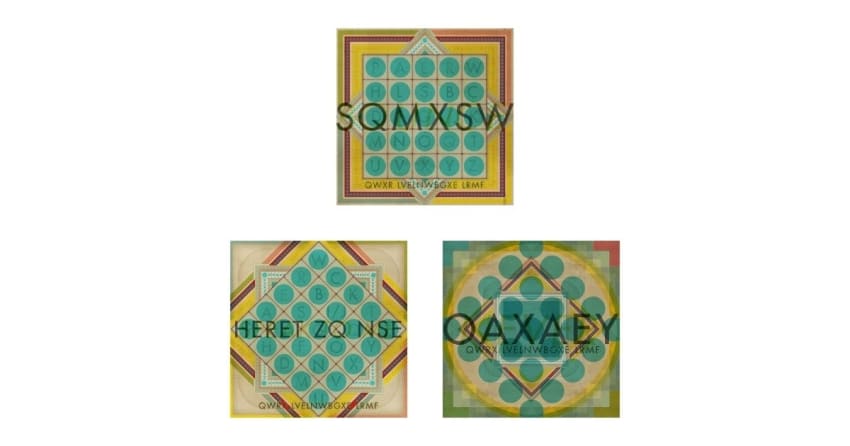
Many design elements in the first indecipherable image that came with “Bounce” were repeated in the image that came with “Speak To Me,” namely the five by five table of letters and the string of text at the bottom of the covers. “Never” featured a similarly styled title but the table and repeated text were removed in favor a starker design. After closer inspection and some amateur sleuthing it’s become clear the artwork is based on a secret code –a secret code we’ve cracked.
The Reddit Phish page led to a post on the Reddit Puzzles forum where users identified the artwork’s implementation of the Playfair Cipher. The substitution based code is generated from a keyword patterned table, and in this case relies on the keywords “Paper Wheels” –which you can see represented without repeating any letters (“PAERWHLS”) in the artwork in the table’s top two rows. The table is then completed with the rest of the alphabet according to a few other rules.
Here’s how Wikipedia describes utilizing the Playfair Cipher:
To generate the key table, one would first fill in the spaces in the table with the letters of the keyword (dropping any duplicate letters), then fill the remaining spaces with the rest of the letters of the alphabet in order (usually omitting “Q” to reduce the alphabet to fit; other versions put both “I” and “J” in the same space). The key can be written in the top rows of the table, from left to right, or in some other pattern, such as a spiral beginning in the upper-left-hand corner and ending in the center. The keyword together with the conventions for filling in the 5 by 5 table constitute the cipher key.
To encrypt a message, one would break the message into digraphs (groups of 2 letters) such that, for example, “HelloWorld” becomes “HE LL OW OR LD”, and map them out on the key table. If needed, append a “Z” to complete the final digraph. The two letters of the digraph are considered as the opposite corners of a rectangle in the key table. Note the relative position of the corners of this rectangle. Then apply the following 4 rules, in order, to each pair of letters in the plaintext:
1. If both letters are the same (or only one letter is left), add an “X” after the first letter. Encrypt the new pair and continue. Some variants of Playfair use “Q” instead of “X”, but any uncommon monograph will do.
2. If the letters appear on the same row of your table, replace them with the letters to their immediate right respectively (wrapping around to the left side of the row if a letter in the original pair was on the right side of the row).
3. If the letters appear on the same column of your table, replace them with the letters immediately below respectively (wrapping around to the top side of the column if a letter in the original pair was on the bottom side of the column).
4. If the letters are not on the same row or column, replace them with the letters on the same row respectively but at the other pair of corners of the rectangle defined by the original pair. The order is important – the first letter of the encrypted pair is the one that lies on the same row as the first letter of the plaintext pair.
To decrypt, use the INVERSE (opposite) of the last 3 rules, and the 1st as-is (dropping any extra “X”s, or “Q”s) that do not make sense in the final message when finished).
Developed in 1854 by Charles Wheatstone, the cipher was used by the British military in both World Wars before modern technology rendered it too easily cracked. Deciphering the TAB artwork code was fairly straightforward using this tool, entering “PAERWHLS” as the keyword, choosing the “Replace J with I” option, entering “SQVMSW” –the text from the “Bounce” cover –and resulting in the decoded “BOUNCE.” The repeated text, “QWXR LVELNWBGXE LRMF” decodes to “TREY ANASTASIOX BAND” (the extra “x” adheres to the cipher’s rules), while “HERET ZQ NSE” becomes “SPEAK TO MEX” and “OAXAEY” becomes “NEVERX.”
In what might also be a hidden message for those who aren’t colorblind, the decoded text is also faintly written in light yellow font behind the encoded words in each image. We reached out to Trey for some insight on the secret language, here’s what he had to say, “Iyay avehay onay ideayay atwhay youyay areyay alkingtay aboutyay.”
